The Federal Deposit Insurance Corporation (FDIC) today announced that JustProtect was one of six teams chosen to participate in a ‘tech sprint’ designed to explore new technologies and techniques to determine how well community banks, and the banking sector as a whole, can withstand a major disruption of any type.
Recent Posts
FDITECH Selects JustProtect as potential solution for Banks to Measure and Test Resiliency
Oct 4, 2021 2:45:48 PM / by Vikas Bhatia
Why International Women's Day is important at JustProtect
Mar 8, 2021 4:27:22 PM / by Vikas Bhatia posted in CEO, Startups
“My father used to have an Attarr (natural perfume oil) shop”, Nanny recalled. She raised me on tales of how she, as a little girl she was allowed to be in her father’s shop to help with customers and even listen in on business meetings. When I questioned how she learned English, she told my sister and me that she taught students English in a local college. We didn’t question these stories; however, they seem extremely progressive for a pre-partition 1930’s India.
JustProtect named Tampa Bay's Inno on Fire honoree
Oct 16, 2020 7:30:00 AM / by Vikas Bhatia posted in Tampa
JustProtect is excited to announce that it has been considered an innovator that's "heating up" Tampa Bay's tech and startup scene.
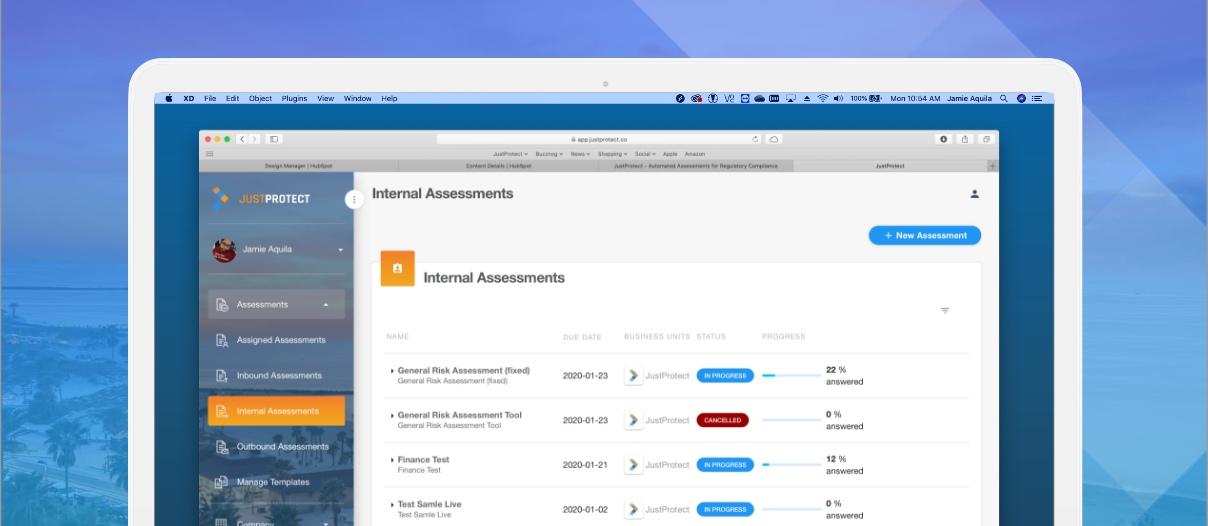
What's wrong with Enterprise Vendor Assessments?
Sep 23, 2020 2:10:12 PM / by Vikas Bhatia posted in assessments, enterprise, vendor
It was reported that contractors in China used by Microsoft to train Cortana, their AI engine, were granted access to voice recordings with minimal cybersecurity controls. A former contractor told the Guardian that workers were not vetted and shared account credentials were able to be used on personal laptops.
Startup CEOs considerations in the post COVID world.
Jul 7, 2020 12:19:37 PM / by Vikas Bhatia posted in CEO, compliance, Strategy, assessments, working remotely, Raising money
Preparing to return to work after COVID-19 Crisis
Jun 12, 2020 2:30:00 PM / by Vikas Bhatia posted in cybersecurity, Strategy, assessments, telework, working remotely, COVID-19
Preparing for Risk
JustProtect is known for our ability to make cybersecurity and vendor risk assessments easier. But we, just like everyone else, have broader concerns from a risk perspective.
When COVID-19 arrived on our shores, it forced a large portion of the country's employees to work from home. While the majority of our team already worked remotely, we still needed to advise one of our office locations to work from home.
COVID-19 JustProtect CEO Update
Mar 16, 2020 1:05:45 PM / by Vikas Bhatia posted in CEO
How are Cybersecurity Experts thinking about COVID-19?
From the time that I started my Cyber, or Information, Security in the early 2000's career one of the fundamental tenants that was drummed into me was that human safety and security is placed higher than the safety and security of data and technology.
Selling to Defense Organizations? Get introduced to DFARS
Jan 17, 2020 3:58:44 PM / by Vikas Bhatia posted in compliance, assessments, dfars, 800-171
Throughout its history, the Department of Defense (DOD) has relied on contractors, these are individuals or non-federal companies that supply services, supplies, or construction. Almost all of these relationships involve the sharing of sensitive information which could present some sort of risk.
Finally, a New years resolution you can commit to!
Jan 7, 2020 11:00:00 AM / by Vikas Bhatia posted in CEO, Strategy

How do I start a vendor management program?
Jan 6, 2020 11:38:06 AM / by Vikas Bhatia posted in compliance, assessments, 3rd party
You've probably heard how important vendor management is to the success of your information security program. But it's important that you learn how to start a vendor management program and perform assessments for it so that each assessment supports your business.