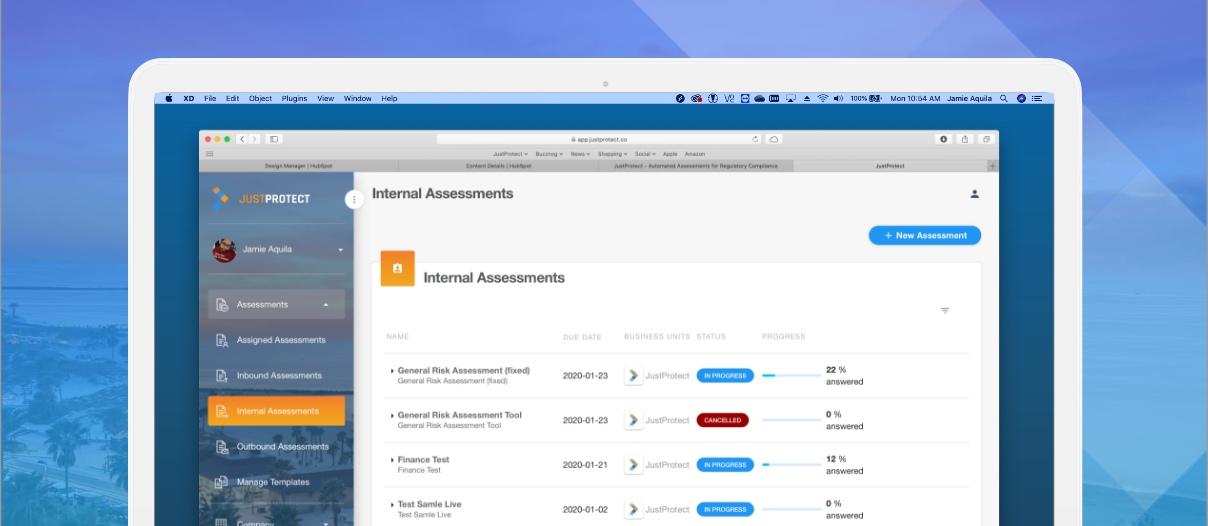
Being the Information Security Manager at a startup, I have to be able to demonstrate to our CEO that we have acted on critical vulnerabilities. It also means that I have to be quick and efficient. Here's how I assess all of our third parties under 60 seconds using our platform:
How JustProtect assesses 100% of our third parties
Dec 14, 2021 1:40:26 PM / by Bryan "SOC" Urias posted in compliance, vendor, Risk Assessor, Security, Log4j
Navigating the Manual Maze and Legacy GRC Systems
Apr 21, 2021 9:00:00 AM / by Haley Keitel posted in compliance, assessments, 3rd party, vendor, grc
Last week, we discussed the two strategy pitfalls companies face when they realize that they have regulations, laws, and certifications they need to be in compliance with. This post dives deeper into what companies experience when they go down this path.
What's wrong with Enterprise Vendor Assessments?
Sep 23, 2020 2:10:12 PM / by Vikas Bhatia posted in assessments, enterprise, vendor
It was reported that contractors in China used by Microsoft to train Cortana, their AI engine, were granted access to voice recordings with minimal cybersecurity controls. A former contractor told the Guardian that workers were not vetted and shared account credentials were able to be used on personal laptops.