SolarWinds is facing a continued lawsuit from investors that has specifically named the CFO and now the CISO, as a result of their lack of disclosure controls and systems surrounding their cybersecurity risk management following a major breach.
Why the SolarWinds Lawsuit should concern CFOs as well as CISOs
Aug 20, 2021 10:00:00 AM / by Haley Keitel posted in cybersecurity, Security, CISO, CFO, data breach
10 tips for cybersecurity professionals
Aug 19, 2021 2:00:00 PM / by Haley Keitel posted in cybersecurity, Strategy, Security, CISO
We want to equip you with tips on how to markedly improve efficacy in your role. While these tips are general enough to apply to anyone in security, we find that they are geared towards anyone fresh to the industry or new in a cybersecurity role
Read on for our top ten tips for cybersecurity professionals like yourself.
3 ways to simplify cybersecurity and risk management without the anxiety
Jul 21, 2021 5:00:00 PM / by Haley Keitel posted in compliance, cybersecurity, 3rd party, Risk Assessor, Security, privacy
Here are three quick ways to simplify your risk management processes without increasing your anxiety or your costs.
Why a company like yours doesn't need a fully formalized ISMS.
Jul 7, 2021 1:21:01 PM / by Bryan "SOC" Urias posted in cybersecurity, Strategy, dashboards, Security
An Information Security Management System (ISMS) is simply a framework for information security practices within your organization. You may immediately jump to think about a full set of policies and procedures, several stacks of network appliances, certifications, and an endless number of hoops to jump through.
The good news is that you don’t have to start there, the most important step is not the first step or the last step. It’s the next step. You can simply begin using risk-based strategies to build your ISMS one layer at a time.
First American Financial Corporation Enforcement
Jun 30, 2021 3:19:25 PM / by Haley Keitel posted in compliance, cybersecurity, Policy, Security
First American Financial Corporation (FAFC) is facing the first-ever penalty from the SEC in the form of a cease-and-desist order and civil fines, as a result of their lack of disclosure controls and systems surrounding their cybersecurity risk management.
How assessments can prevent ransomware
Jun 21, 2021 4:48:04 PM / by Haley Keitel posted in cybersecurity, assessments, Security, ransomware
Ransomware is not isolated to tech companies, which is clearer than ever given the attacks this year. In a recent interview with Now This, our CEO Vikas Bhatia, discussed the fundamentals of these attacks and how companies across industries can better prepare by utilizing a third-party risk management plan.
Resolving Your 3rd Party Assessment Needs
May 4, 2021 11:15:00 AM / by Jamie Aquila posted in cybersecurity, assessments, 3rd party
Now that we have identified the issues to watch out for, we can share what you can do to triage risks and develop your 3rd Party GRC Solution.
Old vs. New Thinking in 3rd Party Assessments
Apr 27, 2021 9:00:00 AM / by Jamie Aquila posted in compliance, cybersecurity, assessments, 3rd party, grc
Let’s Reassess How You Think About 3rd Party Assessments!
Caveat: We can’t possibly provide a complete 3rd Party consulting framework in a short blog. This post is to provide you with a new framework for 3rd Party risk and new thinking in assessments.
First, let’s clearly define what a 3rd Party is. We believe they encompass all of the following: suppliers, 3rd Party agents, contractors, distribution centers, call centers, contract manufacturers or assemblers, outsourcing firms, service providers (SaaS, Cloud, and a thousand more).
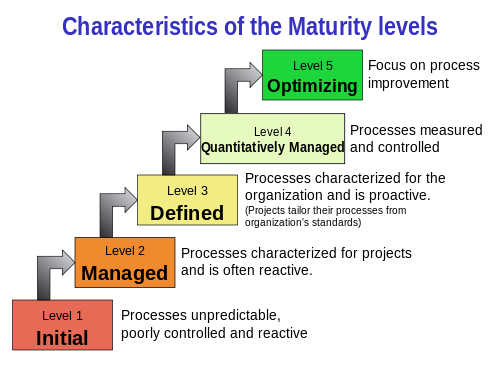
What exactly is the CMMI Scale?
Oct 15, 2020 11:40:00 AM / by Jamie Aquila posted in cybersecurity, enterprise, cmmi
Clients of all shapes and sizes receive inbound assessments from much larger organizations with something strikingly similar to one another: they all use this 5 point scale that makes no sense to smaller companies. Initial? Managed? What do these all mean?
Let’s help explain to you what these are.
Special Announcement! Upcoming Blog Series-All About Assessments
Jul 13, 2020 10:58:48 AM / by Jeffery Ratliff posted in CEO, compliance, cybersecurity, assessments, 3rd party
Regulatory compliance can be a daunting task for small companies for a variety of reasons. For some, it could be that they do not have the necessary staff to commit to such a project. For others, it may be the lack of capital to pay an expensive consultant to do it for them. Another issue that plagues small companies is the lack of knowledge required to navigate the treacherous waters of regulatory compliance. While JustProtect may not be able to provide your company with more employees or extra money, something we can give you is knowledge. And Knowledge is Power.