Transforming the
Assessment Lifecycle.
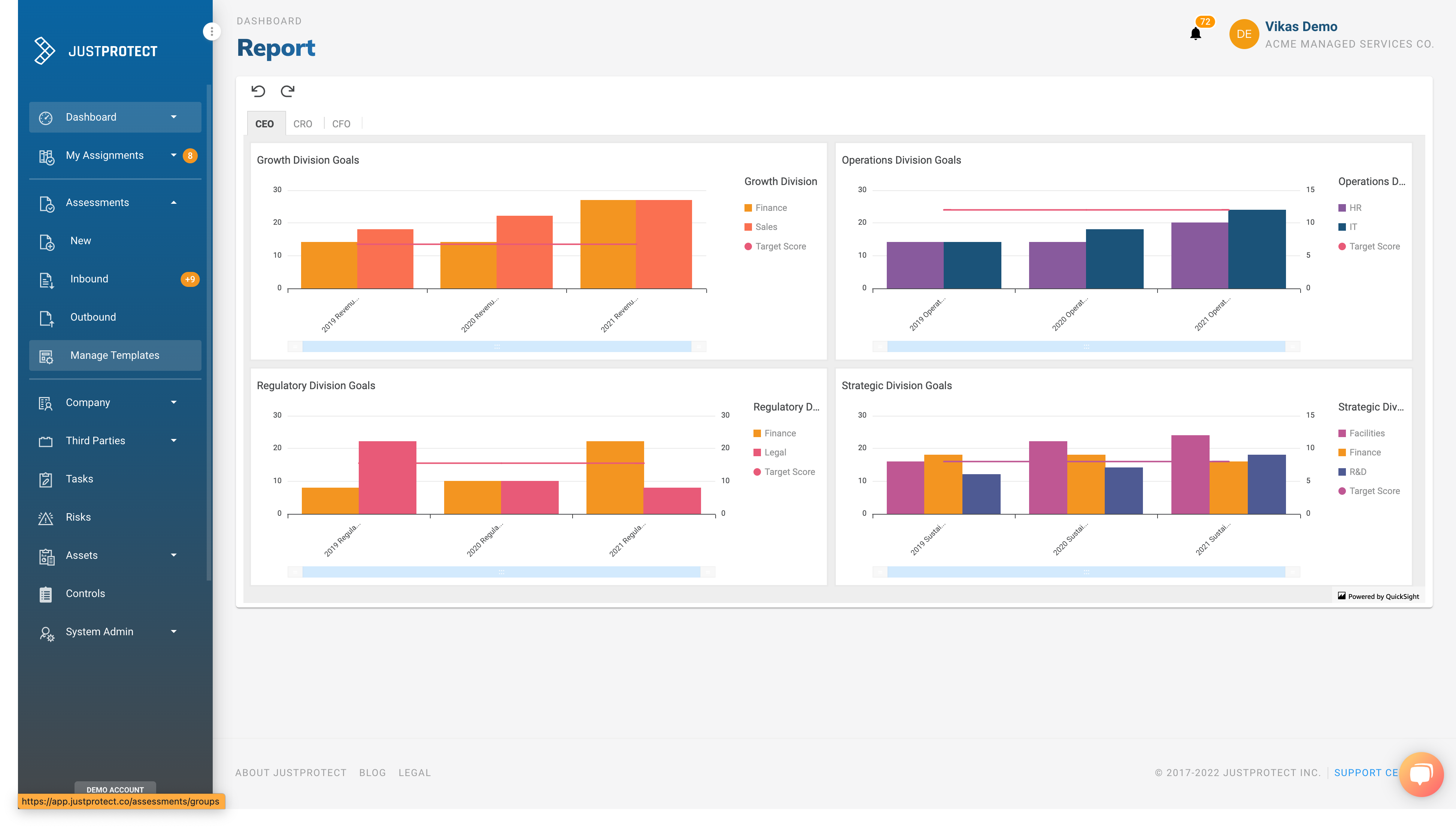
JustProtect enables you to automate and scale the Assessment Lifecycle to reduce time, increase productivity, and bridge communication gaps both across functions and the organization as a whole.
JustProtect produces a level of clarity leading to increased confidence and better investment decisions.
JustProtect helps organizations who may be struggling with complex and inefficient assessment management across teams, departments and external stakeholders.
By automating the 'busy work' associated with managing the end-to-end assessment process, we allow our customers to focus on
"JustProtecting" their business.
What our customers are saying...
“Before JustProtect, we were disorganized, repeating the requests of evidence, and unable to keep on top of the 4 audits we managed a year -- and that was with a GRC system! With JustProtect, we're now able to stay on top of Infosec's activity and automate our reporting to the business stakeholders."
“Since the SEC released the proposed cybersecurity hygiene and incident disclosure rules, our Board, legal and compliance stakeholders are paying a lot more attention. With JustProtect, we have the ability to organize the entire reporting process while saving countless man days every quarter.”
“We engaged with a well-known consulting firm to prepare for our IPO. They delivered a 127-page report for us to work through. By using JustProtect, we were able to organize all the observations, risks, projects and tasks so that the entire team could work asynchronously. I don't know what I would have done otherwise!"
Got Questions?
Is JustProtect a GRC, a workflow solution or survey platform?
JustProtect is an enterprise Assessment Lifecycle Platform that facilitates the decision making process. The problem we solve is much broader than Governance, Risk or Compliance, Operations or Analytics which makes it the right system to solve this problem. JustProtect is a level down in the stack from today's solutions, traversing typical organizational silos.
What if we already have a GRC, workflow solution or survey platform?
It's not unusual for JustProtect customers to have one or multiple solutions. We co-exist with them all! We believe that businesses should have a single system that is the "connective tissue" between cybersecurity and all other departments that need to be involved in an enterprise decision-making process.
Who are the typical users of JustProtect?
Cybersecurity teams typically own the JustProtect platform, however we bring together cybersecurity data and make it business-relevant for anyone - legal, finance, compliance or the Board - to meet complex regulatory requirements and ultimately make better decisions for the organization
What frameworks does JustProtect work with best?
We have future-proofed our Platform to support any framework, regulation or standard whether that was developed in-house or by organizations such as the SEC, ISO, AICPA, NIST, or CIS.
How does the JustProtect time-to-completion compare with other 3rd party risk assessment solutions?
Today, a 3rd party risk assessment takes ~6 weeks to complete, end-to-end. With JustProtect, our customers can facilitate the same Assessment in less than 72 hours with more than 50% added capacity to an existing team within weeks of onboarding. Our solution returns a positive ROI within weeks due to the speed and scale the assessments can be facilitated.
What are some of the challenges the JustProtect Platform addresses?
- Assessments that need to be redesigned to accommodate business processes and workflows to address emerging cybersecurity regulations.
- Inefficient assessment processes that negatively impact revenue generation, compliance posture and investor confidence.
- Legacy GRC solutions that were designed for “vertical” silos thereby making them inflexible and requiring significant resources to implement and operate.
- Spreadsheets and emails that are used to overcome the incomplete business processes between GRC and enterprise applications resulting in multiple “records of truth”.
Why do higher education organizations need to conduct risk assessments?
Reputational Risks: Higher education institutions rely on their reputation to attract students, faculty, and donors. Risks such as data breaches or financial mismanagement can damage an institution's reputation and negatively impact enrollment and funding.
Operational Risks: Higher education organizations have complex operations, with many different departments, programs, and activities. Conducting risk assessments can help identify potential issues that could disrupt operations and impact the organization's ability to function effectively.
Financial Risks: Higher education organizations often have large budgets and significant financial resources, and they can be exposed to financial risks such as fraud, financial mismanagement, or
How does JustProtect transform the Assessment Lifecycle?
With JustProtect, you can automate and scale the Assessment Lifecycle to reduce time, increase productivity, and bridge communication gaps both across functions and the organization as a whole.
What are some of the consequences of a fragmented, decentralized approach to managing assessments?
Fragmented, decentralized assessments can:
- Lead to redundant efforts, wasted resources and increased costs as teams and departments duplicate efforts or work in isolation
- Cause delays, bottlenecks and inconsistencies hindering prompt decision-making and operational efficiency
- Result in compliance gaps and increased risks due to overlooked or inconsistently addressed regulatory requirements
- Create communication barriers between cybersecurity and business executives, impairing effective collaboration and compromising business protection.
Stay informed!
Subscribe for updates and the latest industry news from JustProtect!